
Why does it require multiple certificates for my vCenter server?#
In short, each service requires a certificate because it could feasibly be on a server (or servers) of it’s own - take this hypothetical design - each role is hosted on it’s own VM, and there are 7 certificates required - SSO, Inventory Service, vCenter Server, Orchestrator, Web Client, Log Browser and Update Manager. If you install all these services on one server you still have to create certificates for those individual services.

Why install valid certificates at all - it “works” with the self-signed ones!#
Well yes, it does work - but so does entering a blank password. That doesn’t mean it’s a good idea! This goes back to a fundamental understanding of what SSL does - it provides a method to secure communications between a server and a client, whether that client is another server, the same server or your vSphere Client on your laptop. In effect, the certificate says “this is who I am, this is who vouches for my identity”, the Certificate Authority acts as the 3rd party that vouches for the server’s identity. If you use a self-signed certificate you have a situation where “this is who I am, and I say so”!
With a self-signed certificate you can get into the bad habit of just clicking “Ignore” on a certificate warning:
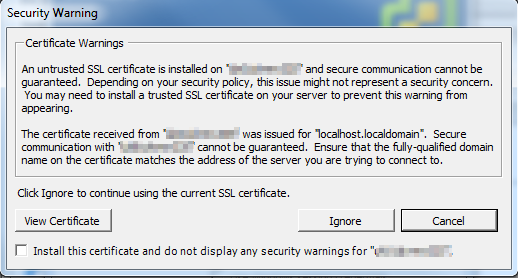
I think the key line in this warning is “Secure communication with
OK, so it’s a “best practice” - but isn’t the risk low? Is it worth the effort?#
At the end of the day it’s your call - but it’s a best practice for a reason. To me security is always about mitigating risks and you have to ask yourself whether a few hours to secure your hosts is worth it. In my opinion, a good strong unique password will cost you more time over a year than installing certificates - but you wouldn’t dream of using a blank password would you?! There are tools out there like the VMware Certificate Automation Tool, and plenty of helpful walk-through’s available that make it a lot less painful now.
There are also strong hints from VMware that tools like PowerCLI will be less lenient by default in future releases, which can only be a good thing.
Isn’t it time you considered securing your Virtual Environment?
