This is the second article in a series of vSphere Security articles that I have planned. The majority of this article is based on vSphere/ESXi 5.1, though I will include any 5.5 information that I find relevant. The first article in this series was vSphere Security: Understanding ESXi 5.x Lockdown Mode.
This is the second article in a series of vSphere Security articles that I have planned. The majority of this article is based on vSphere/ESXi 5.1, though I will include any 5.5 information that I find relevant. The first article in this series was vSphere Security: Understanding ESXi 5.x Lockdown Mode.
Why would you want to join an ESXi host to an Active Directory domain? Well you’re not going to get Group Policies applying, what you’re really doing is adding another authentication provider directly to the ESXi host. You will see a computer object created in AD, but you will still need to create a DNS entry (or configure DHCP to do it for you). What you will get is a way to audit root access to your hosts, to give administrators a single sign on for managing all aspects of your virtual environment and more options in your administrative arsenal – for example, if you’re using an AD group to manage host root access, you don’t have to log onto however many ESXi hosts you have to remove a user’s permissions, simply remove them from the group. You can keep your root passwords in a sealed envelope for emergencies! 😉
Joining a domain#
You can join an ESXi host to an AD domain via the Web Client, vSphere Client or using PowerCLI. There are a couple of prerequisites, obviously you need an AD domain(!) and you need to make sure that to host’s DNS name matches the AD DNS name – e.g. my AD is “definit.local”, so the ESXi host esxi01 needs to be esxi01.definit.local. You need to point the ESXi host to the DNS server that is hosting your AD DNS zone and you need to ensure the either your hosts are using the Domain Controller as a time source (OK) or your Domain Controller and the ESXi hosts are both using the same external secured time source (better!).
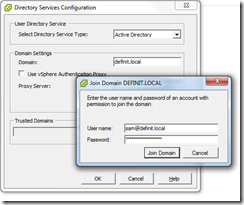
In the vSphere Client, select a host, go to the Configuration tab and then the Authentication Services page. Click on Properties… to open the dialogue and select “Active Directory” in the “User Directory Service” section. Enter the DNS name of the domain in the “Domain” field and click “Join Domain”. You should be prompted for credentials to join the domain, so you need to enter an AD account with permissions to add computers. Once joined, the same dialogue will allow you to leave the domain via the “Leave Domain” button. You can specify the OU that the computer object is created in by using the format of dns.name/OU/Path – so I used definit.local/Servers/ESXi. Interestingly I found that it didn’t like a deep OU path, and the Web Client would not accept an OU path at all.
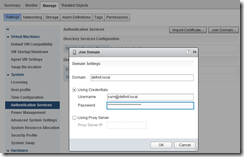
Similarly, using the Web Client you can select a host, go to the “Manage” tab and select “Authentication Services”. Click “Join Domain…” and enter the details there. As I mentioned above, adding an OU path doesn’t seem to work here.
To join a domain using PowerCLI you need to use the following command:
Get-VMHost ESXi01.definit.local | Get-VMHostAuthentication | Set-VMHostAuthentication -Dom
ain definit.local/Servers/ESXi -JoinDomain –Username [email protected] –Password Passw0rd!
I’ve not been able to get the PowerCLI to disjoin a server from the domain, but the syntax is similar:
Get-VMHost ESXi01.definit.local | Get-VMHostAuthentication | Set-VMHostAuthentication –LeaveDomain
Configuring Active Directory Authentication#
So now the host is connected to AD…what next? By default ESXi will look for a group called “ESX Admins” and add it to the local Administrators role – this grants any members of this group full administrator access. This might not be a desired configuration – for example, I manage ESXi hosts for the EMEA, but there are also North America, Asia Pacific and Latin America and other regions – we can’t all use “ESX Admins” on the same domain! Fortunately there are some advanced configuration settings available:
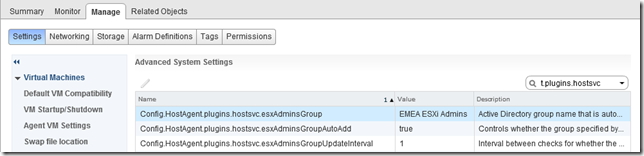
You can disable the auto-add feature by setting the Config.HostAgent.plugins.hostsvc.esxAdminsGroupAutoAdd configuration to “false” on each host.
You can specify a different group by setting the Config.HostAgent.plugins.hostsvc.esxAdminsGroup value – in my case I used “EMEA ESXi Admins”
By default ESXi will check that group once a minute – you can modify that interval up to 30 minutes if you so desire, that’s also in the same place: Config.HostAgent.plugins.hostsvc.esxAdminsGroupUpdateInterval
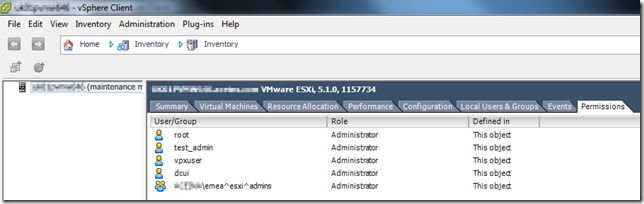
If you connect to the host directly with the vSphere Client, you should see your group added to the permissions tab (here’s no way to do this via the Web Client as it requires a direct connection):
You can now also add domain users directly to roles on the ESXi host in the same way you would add local users (e.g. go to the permissions tab, right click and “Add Permission…” – select “Add…” and find the user in the domain, then assign a role.
You can now use your AD credentials to connect directly to the host via vSphere Client or PowerCLI with Windows session credentials, or your UPN (e.g. [email protected]) for SSH and the DCUI.