 As a PowerShell fan I find using the vCO PowerShell plugin makes my life a whole lot easier. What isn’t easy however, is the configuration of vCO and a PowerShell jump host. Having done it a few times, this is my method for ensuring a secure working connection using HTTPS and Kerberos.
As a PowerShell fan I find using the vCO PowerShell plugin makes my life a whole lot easier. What isn’t easy however, is the configuration of vCO and a PowerShell jump host. Having done it a few times, this is my method for ensuring a secure working connection using HTTPS and Kerberos.
Configure the Orchestrator Appliance#
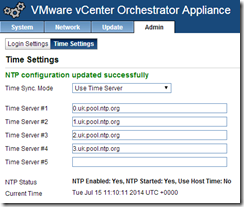
Since we’re planning on using Kerberos authentication, we’d better ensure that the time is correct AND syncs to the same source as the domain.
In order to configure Kerberos on the Orchestrator appliance you need to SSH in to the box and log in using your root credentials.
Create a new krb5.conf file under /usr/java/jre-vmware/lib/security/ using the following command:
vi /usr/java/jre-vmware/lib/security/krb5.conf
Enter the following, substituting your domain details, and the local domain controller for “kdc =”. Case is important here, so use caps where I have:
[libdefaults]
default_realm = DEFINIT.LOCAL
[realms]
DEFINIT.LOCAL = {
kdc = dc-01.definit.local
default_domain = definit.local
}
[domain_realms]
.definit.local=DEFINIT.LOCAL
definit.local=DEFINIT.LOCAL
[logging]
kdc = FILE:/var/log/krb5/krb5kdc.log
admin_server = FILE:/var/log/krb5/kadmind.log
default = SYSLOG:NOTICE:DAEMONIf the krb5.conf file did not exist, change the permissions to allow the system to read the file:
chmod 644 /usr/java/jre-vmware/lib/security/krb5.conf
Configure the PowerShell host#
I’m configuring to use HTTPS with Kerberos authentication, so the first thing I need is a certificate with the Server Authentication (1.3.6.1.5.5.7.3.1) key usage. If you’re running a Microsoft PKI, the default Computer certificate template is perfect for this.
Open MMC and add the Certificates snap in for the Computer account, find your certificate and double-click to open. Select the Details tab and scroll to the bottom – copy the thumbprint value to use in the below command.

Enable WinRM with the following command:
winrm quickconfig
Increase the amount of memory allowed to be allocated to each executing PowerShell:
winrm set winrm/config/winrs @{MaxMemoryPerShellMB="2048"}Create an HTTPS listener using the thumbprint and the following command:
winrm create winrm/config/Listener?Address=*+Transport=HTTPS @{Hostname="host_name";CertificateThumbprint="certificate_thumbprint"}

Finally, enable Kerberos authentication:
winrm set winrm/config/service/auth @{Kerberos="true"}The PowerShell host is now listening on port HTTPS 5986 authenticated by Kerberos!
Test the WinRM connection#
Using another computer on the same domain, run the following command to execute NSLookup on the PowerShell host:
winrs –r:https://mgmt-01.definit.local:5986 nslookup google.com

Adding a PowerShell host#
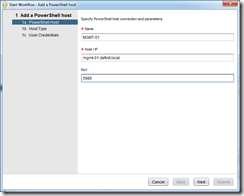
The final step is to add a PowerShell host to Orchestrator. Open (or install first and then open) the Orchestrator client and connect to your vCO appliance. Make sure you’re connecting using your domain account (i.e. you need to pass your domain identity to the vCO appliance to use for authentication to the PowerShell host).
Specify a name for the PowerShell host (the hostname of the server is fine), the FQDN (best to use FQDN with Kerberos) and the port that we created the listener on – 5986 by default.
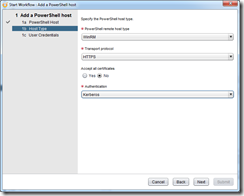
Select WinRM as the host type, HTTPS and do not accept all certificates, finally select Kerberos authentication.
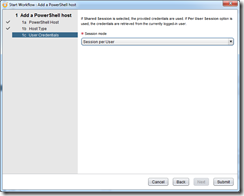
Select “Session per user” to configure the remote host to use the workflow user’s identity. You can enter credentials for a shared session, but this could pose security risks if running as an elevated user.
Finish the wizard and wait until the workflow completes:
Now we have a PowerShell host added to vCO, we can run a PowerShell script against it over HTTPS and authenticated with Kerberos.
Running a Hello World PowerShell script in vCO#
Firstly, lets create “Say-HelloWorld.ps1” script and save it in c:\SCRIPTS on the PowerShell host.
return “Hello World”
Next switch back to the Orchestrator client and select “Design” mode. Create a new folder to contain your workflows (mine is called “DefinIT”) and then create a new workflow (“Test-PowerShell-Hello-World”).
Select the “Workflow” tab and then expand “All Workflows” > Library > PowerShell, then drag the “Invoke an external script” onto the workflow editor:
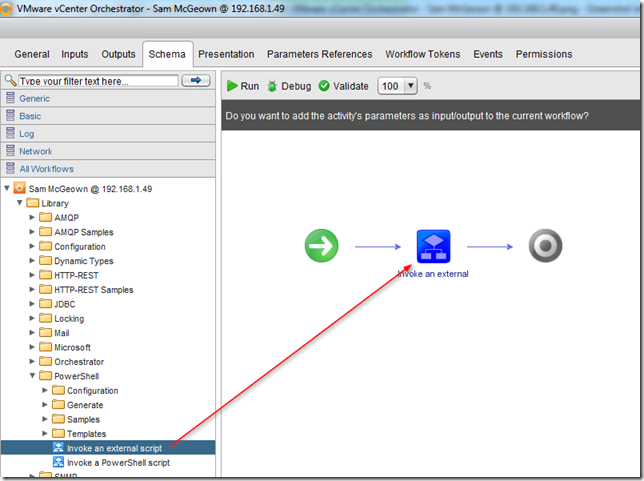
Click on the “Setup” button:

Select the value radio button for the “host” binding and then click to select the PowerShell host from the inventory. Select value for the “externalScript” binding and enter the path to the hello world script we created earlier. Select script for the arguments, as we don’t have any. Leave the output binding as is.

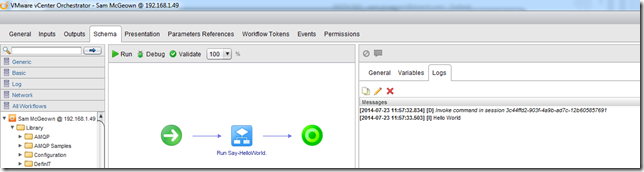
Now we can run the workflow and select the “Logs” tab to see the output – you can see the “Hello World” that we returned is echoed in the logs.
Hopefully this has been a helpful kick-starter into using vCO PowerShell over HTTPS with Kerberos Authentication
