vcenter
 Written by Sam McGeown
on 21/9/2018
Written by Sam McGeown
on 21/9/2018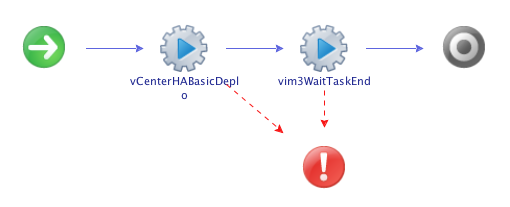 Just a quick post today to cover a new vRO action and workflow I’ve uploaded to GitHub that configures vCenter High Availability in the basic mode. This is based on William Lam’s excellent PowerShell module that does the same, but using vRO. I also hope to release a version for the advanced mode based on my PowerShell script in the near future.
TL;DR - package is availabile on GitHub
The workflow itself is pretty self explanatory, with my deployment action, which returns a VC:Task, and the standard “wait for a task to end” action.
Just a quick post today to cover a new vRO action and workflow I’ve uploaded to GitHub that configures vCenter High Availability in the basic mode. This is based on William Lam’s excellent PowerShell module that does the same, but using vRO. I also hope to release a version for the advanced mode based on my PowerShell script in the near future.
TL;DR - package is availabile on GitHub
The workflow itself is pretty self explanatory, with my deployment action, which returns a VC:Task, and the standard “wait for a task to end” action. Written by Sam McGeown
on 1/7/2014
Written by Sam McGeown
on 1/7/2014Recently I encountered this problem in a customer site whereby the logon to VCSA 5.5 would either time out, or take 3-5 minutes to actually log on.
Running a netstat on the VCSA during the attempt to logon showed there was a SYN packet sent to the vCOps appliance on port 443 that never established a connection. Another check was attempting to connect using curl <https://> –k - this would time out.
 Written by Sam McGeown
on 10/1/2014
Written by Sam McGeown
on 10/1/2014Published under VMware and vRealize Operations
There’s no doubt that vCOps is a great product for proactively monitoring your vSphere environment, but it’s a hefty package for the lab. The minimum recommended RAM is a whopping 16GB – in my lab that’s the whole of my management host! I recently needed to do some testing so I wanted to get it running in the lab with the barest minimum I could get working, and it turns out you can get working with just 4GB and 2 CPU…albeit you wouldn’t want to monitor much!
 Written by Sam McGeown
on 11/6/2013
Written by Sam McGeown
on 11/6/2013The vSphere UMDS provides a way to download patches for VMware servers that have an air-gap, or for some reason aren’t allowed to go out to the internet themselves – in my case a security policy prevented a DMZ vCenter Server from connecting to the internet directly. The solution is to use UMDS to download the updates to a 2nd server that was hosted in the DMZ and then update the vCenter Server from there.
 Written by Sam McGeown
on 6/11/2012
Written by Sam McGeown
on 6/11/2012Published under VMware
The process of requesting certificates for vSphere 5.1 is a fairly grim, manual process. It’s repetitive and easy to make a mistake on any step of the way. Since I’ve got to do this for quite a few VirtualCenter Servers, I thought I’d script the certificate generation if nothing else. I am following the excellent documentation provided in Implementing CA signed SSL certificates with vSphere 5.1 and more specifically in Creating certificate requests and certificates for vCenter Server 5.
