vMA is available as a Virtual Appliance (OVF) from VMware. To install it on VMware Workstation 7, open Workstation and select Import or Export to import a new OVF, the URL for the latest OVF for vMA is on the vMA download page

As per this article on virtualkenneth.com, you need to edit the VMX file to change the SCSI card and OS type, otherwise you’ll have a kernel panic on boot.
Once you’ve done that boot the vMA in workstation and check the console, you will be prompted to provide a secure password for the vi-admin user. Once you’ve done that, the network config wizard will start. You can use DHCP to configure the network, then provide a hostname, or you can specify your network settings manually.


The wizard will then reset the network interfaces and bring up the new settings.

To re-run the network config wizard, log onto the console and use the following commands:
cd /opt/vmware/vma/bin
sudo ./wmware-vma-netconf.pl
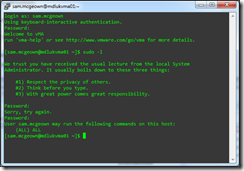
After this, I was able to access my vMA by SSH – PuTTY is my client of choice.
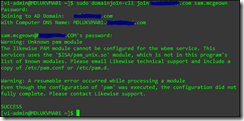
Joining the vMA to the domain for AD authentication#
If you want to use AD authentication with your ESXi hosts, you can join them to the domain – it’s the same with the vMA. To join the vMA use the following command:
sudo domainjoin-cli join
It will then prompt you for the root password (for the sudo) before it prompts for your AD admin password! I had errors with it saying ports weren’t open. The most likely cause for that is time so make sure that your server is running in UTC mode (this matches your ESXi and is compatible with your Domain Controller). These steps are taken from Simon Long at The Slog:
sudo rm /etc/localtime
sudo ln -s /usr/share/zoneinfo/UTC /etc/localtime
If you use NTP to sync your environments time, it might be worth adding in your NTP servers to the vMA.
sudo nano /etc/ntp.conf
Add in your ntp servers under the heading: # Use public servers from the pool.ntp.org project.
Configure ntpd to start on reboot:
sudo /sbin/chkconfig ntpd on
Restart ntpd:
udo /sbin/service ntpd restart
Make sure your NTP servers are reachable:
sudo ntpq -p
The final domain join looks like this (sorry for redaction, one day I will have my own test environment!):
Some ease-of-use tips over at VirtuallyGhetto.com allow you to set a default domain for login, and groups who can sudo.
You will need to edit /etc/likewise/lsassd.conf and uncomment “assume-default-domain = yes” and then save your changes:
sudo vi /etc/likewise/lsassd.conf
You will need to reload the configurations for the changes to take effect by running the following utility:
sudo /opt/likewise/bin/lw-refresh-configuration
Now, you can login by just specifying the username without having to provide the full AD domain name.
Just being able to log in is not much help – the power is being part of the sudoers group. Edit /etc/sudoers using vi-admin account, make sure you use ‘sudo’:
sudo vi /etc/sudoers
Add the following towards the bottom of the file:
%DOMAIN\VMware\ Admins ALL=(ALL) ALL
Note: We’re escaping both the initial back slash and the space – the group is “DOMAIN\VMware Admins”
I’m now able to log in as a domain user, and SUDO:
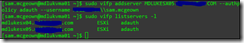
Adding an ESXi Server to the vMA#
To add an ESXi server to vMA is dead simple, especially if your ESXi server is using AD integration too.
sudo vifp addserver
-authpolicy adauth -username DOMAIN\user
You can verify the managed servers using “sudo vifp listservers –l”
Test the connection, and list the NICs
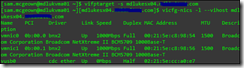
Success!
Conclusion#
The vMA Config guide is great for getting to know and configure the vMA – as is the vma-help command. I’ve linked to articles that helped me along the way, but it’s worth going through the rest of Simon Long’s article and configuring the vMA as a syslog server for your ESXi hosts – they lose their logs on reboot!
